by Jeanne Zepp
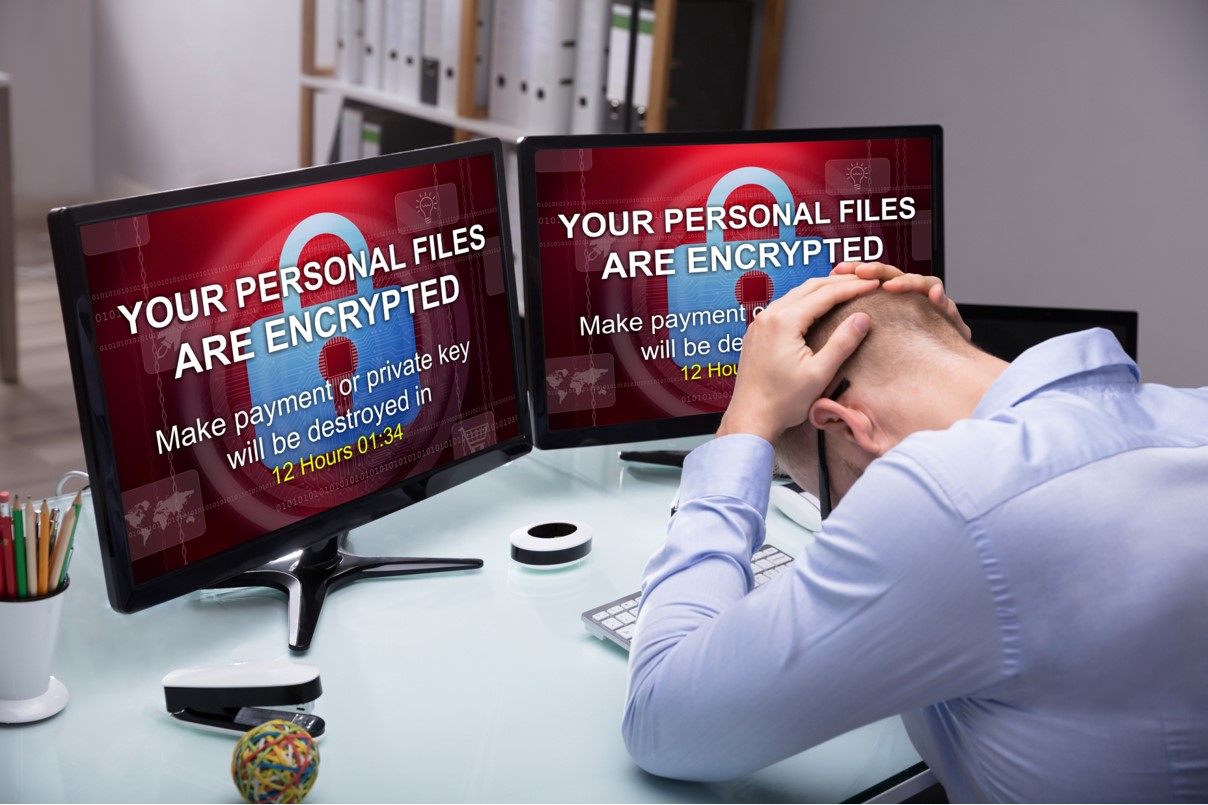
Organizations face a complex decision when their systems are encrypted, their data exfiltrated and their operations brought to a halt. There is no universal prescription for how an organization should respond.
The Federal Bureau of Investigation, Secret Service and other law enforcement agencies are definitive in their opinion: Do not pay the ransom. Seek their assistance rather than contribute to a criminal, money-making scheme that only grows in scope and complexity each year.
Yet, it’s not always that simple. Sometimes, financial considerations prevail. The cost and personnel requirements to rebuild/restore systems from backups may exceed available resources, making the ransom payment seem less expensive in the long run. Other times, because organizations haven’t backed up their data, they see no other business option. For those that bought cyber insurance, covering a ransom payment is one of the reasons why they paid the hefty premiums in the first place.
Then, too, there is the time factor. Consider the dilemma healthcare organizations face. Patient care, especially for the seriously ill, depends on ongoing access to medical records. Any treatment delay could result in catastrophic outcomes for many patients. The pressure to act quickly and decisively can be overwhelming. Many opt to pay the ransom.
Last, there are legal issues surrounding the release of personally identifiable information. Lawsuits and reputational harm are just two negative outcomes. Ransom payments can make those problems go away, often keeping the breach quiet. But, depending on the perpetrator’s locale, it could be illegal to pay a ransom. An organization could be committing a crime of its own in doing so.
IS RANSOM PAYMENT THE SOLUTION?
Ransom payment involves placing trust in a criminal. There are absolutely no assurances that criminals will live up to their end of the bargain. Criminals may or may not furnish a decryptor, and the key may or may not be functional. Paying the ransom may be for naught.
Ransom payment involves placing trust in a criminal.
Similarly, there is no guarantee that the hackers will not return weeks or months later and level another ransom demand. One’s best efforts to cleanse the network post-attack may not eliminate backdoors created for just such a purpose. Plus, cyber criminals now employ what’s been termed a “double extortion” tactic. The organization pays the ransom and regains access. Afterward, a second ransom demand is made: Pay additional monies to assure exfiltrated data is not posted on the internet or sold on the Dark Web.
Other organizations may find some data/files were corrupted and are now unusable, even after using the attacker’s decryption key. Still more may only obtain a partial return of their data.
When dealing with unsavory individuals, ransom payment does not always achieve the desired result or minimize costs. It can add to them.
A MORE REALISTIC SOLUTION
As this discussion illustrates, the true question does not revolve around whether or not to pay a ransom. The real question is, How do I avoid becoming the victim of a ransomware attack and having to confront this untenable decision?
The real question is, How do I avoid becoming the victim of a ransomware attack and having to confront this untenable decision?
Every organization must first recognize that being attacked is not an “if” proposition; it is a question of when. Cyberattack tactics are becoming more sophisticated, in part underwritten by the money extorted via ransom payments. Therefore, prevention is critical, complemented by detection and response capabilities.
Even if you think your organization is prepared, think again. A recent study found that confidence in preparedness is generally misplaced. The data revealed a real disconnect between perceived and actual readiness to deal with a ransomware attack.
There are some steps every organization should take. Prepare a business continuity plan and update it regularly. Stay aware of the latest ransomware attacks and the network vulnerabilities exploited. The Cybersecurity and Infrastructure Security Agency can be instrumental in this regard. Its Shields Up program (see “Are Your Shields Up?” Electroblog) provides regular updates and advisories on cyber threats and free resources and tools for organizations to employ.
Practicing sound cyber hygiene is always the first, best step. It may not eliminate an attack, but it will make it harder for cyber criminals to penetrate a network, limit the scope of the intrusion and quicken recovery time. Some vital steps organizations should take include:
- Timely patch installation
- System segmentation
- Multifactor authentication
- Antiviral and antimalware software
- Endpoint detection
- System monitoring and penetration testing
- Staff awareness training, especially relative to email
- Tabletop exercises to assure response readiness
- Backup and restore process testing
- Backup data storage off-site
Technology use is inescapable. Technology exploitation by criminal elements working on behalf of nation-states or themselves is becoming more pervasive every day. Organizations, regardless of size, need to act proactively to avoid victimization. As always, prevention is the answer.